How vTest Studio and CANoe Tools Empower the Automation of ECU (Electronic Control Unit) Testing
Category : Embedded Blog
From Low-level Device Drivers and Base Software Modules to the upper layers like Application Layer, modern automotive ECUs can have more than 20 million lines of source code.
Manual Testing of the C code (source code), made sense when automotive electronics was in its nascent stage. During those days, the source code was limited to a few hundred lines.
Fast forward to the era of connected car, Automation in Source Code Testing is the only way ahead.
With the help of Automation Testing Tools, software teams are able to deliver more robust quality code along with reduced time-to-market
The word ‘Automation’ is generally related to making a process less time-consuming. However, in case of ‘automation’ in software testing, this switch from manual testing offers some additional value-adds.
We will explore how automation testing tools deliver these value-add. But before that, let’s compare manual testing with automation testing.
Manual Testing v/s Automation Testing: A Snapshot
| Manual Testing | Automation Testing |
| May take one week to 15 days to test a software module of an ECU (Electronic Control Unit). | Can be completed in half an hour or 1 hour |
| Testing multiple signals simultaneously is not possible | Multiple signals can be tested simultaneously using routines (part of code that performs some specific task) |
| Test reports are created manually using excel sheets. | Test reports are created automatically |
| Test-cases are written manually. | Test cases are written using script and can be re-used in other projects as well |
| Each test case must be run separately, thereby, increasing the time for testing | Multiple test cases can run simultaneously on different systems |
| Batch testing (keeping the test cases in queue for execution) is not possible. | Batch testing is possible without any manual interference |
| Performance testing cannot be done accurately | Stress testing, spike testing, load testing can be easily inserted into the test-case script |
How to Set-up Automated Testing Environment Using vTest Studio
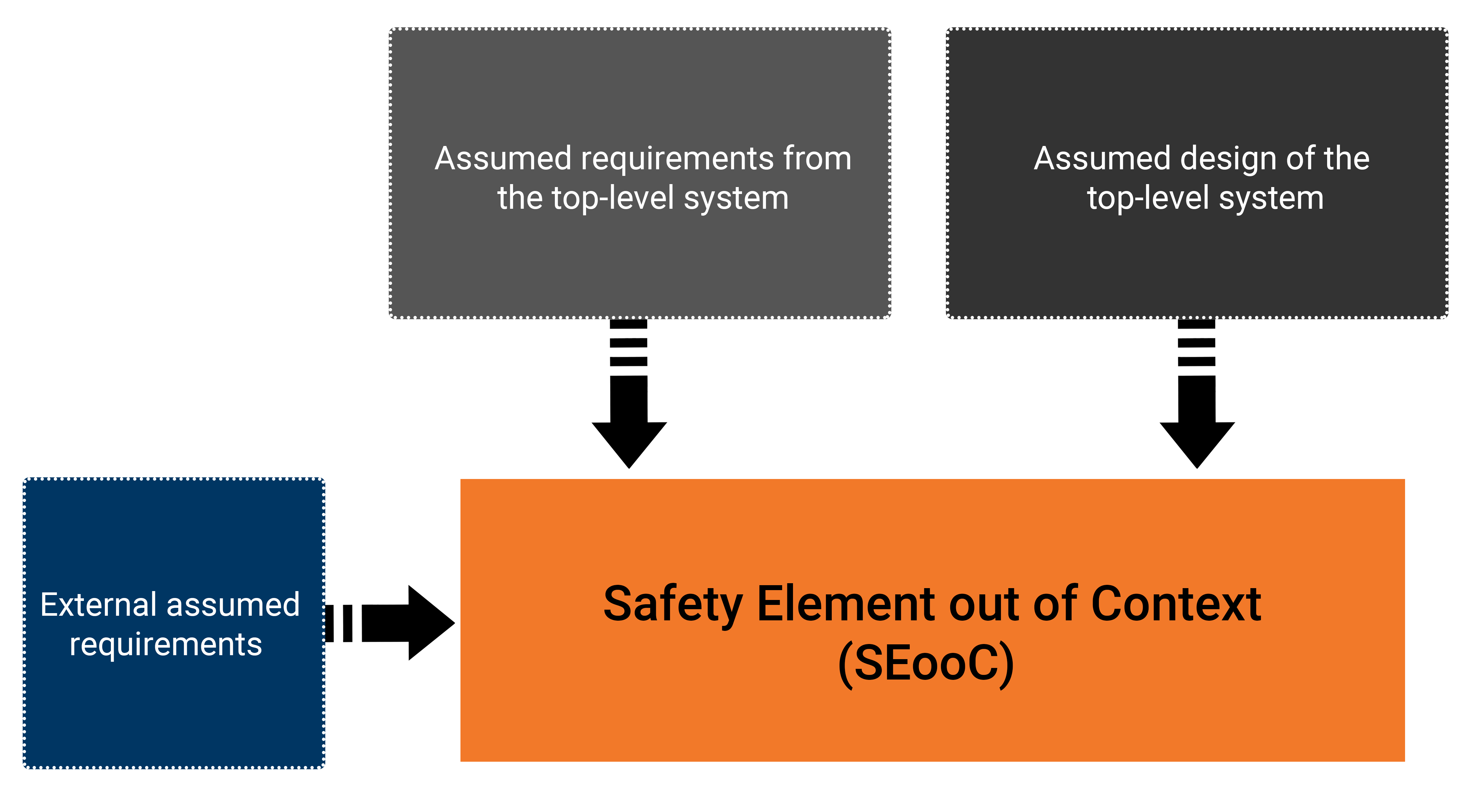
Implementation of automation in testing, for an automotive electronic control unit (ECU), requires a set of tools (both hardware and software).
Essentially, while testing an ECU, we simulate it inside a test bench that mimics the actual vehicle environment.
The target is to validate all the functionalities of the ECU and its behavior against the given requirements.
The set-up should be such that the simulated environment exactly mimics the actual vehicle environment.
In order to set up such a test bench, the following three important components are required:
- vTest Studio– For writing the test cases in CAPL editor
- CANoe Testing tool– For executing the test cases
- CAN Case VN 1600/10/30- Network interface for CAN, LIN, K-Line, IO , in order to understand and visualize communication between the target ECU and the simulated ECU
The three components mentioned above interact with each other to make the automation testing happen. Let’s now understand how they are setup to build a testing environment.
- ECU Pins are connected to the corresponding modules of the CANoe Hardware (CAN Case VN 1600), as per the project requirements. This piece of hardware is connected to the PC
- CANoe Tool is loaded with messages and CAN Databases, that are required for data to be transmitted between the ECUs along with the diagnostics services
- Using the CANoe tool GUI, the modules to be tested are loaded in the CANoe tool
- In the CANoe tool, these modules are configured as per the project requirements
- Now, vTest Studio is initiated and CANoe configuration (performed in step 4) is imported into it.
- The required environment for testing automation is now setup and vTest Studio is ready to design the relevant test cases.
This is the minimum setup required for the automation of the software testing of an automotive ECU (electronic control unit).
After the test cases are created, they are executed on the target control unit and reports are generated.
Now, let’s deep dive and understand this automation in testing better. Let us now discuss about the workflow (step-by-step process) involved in automated testing of a vehicle control unit (ECU).
Understanding the Workflow of the Automated Testing of an Electronic Control Unit (ECU):
Step 1: Creation of Test Cases
- Scripting for test case creation is done in CAPL. It is a programming language very similar to ‘C’. CAPL was created by Vector to test Electronic Control Units using CANoe tool.
- Let’s say you are required to test three modules of an ECU (electronic control unit);viz; – Functionalities, Specifications and Error Handling. The test cases for these three modules will be designed in CAPL editor. All the test cases can be compiled as a single ‘build’ or multiple ones, depending on the modules to be tested.
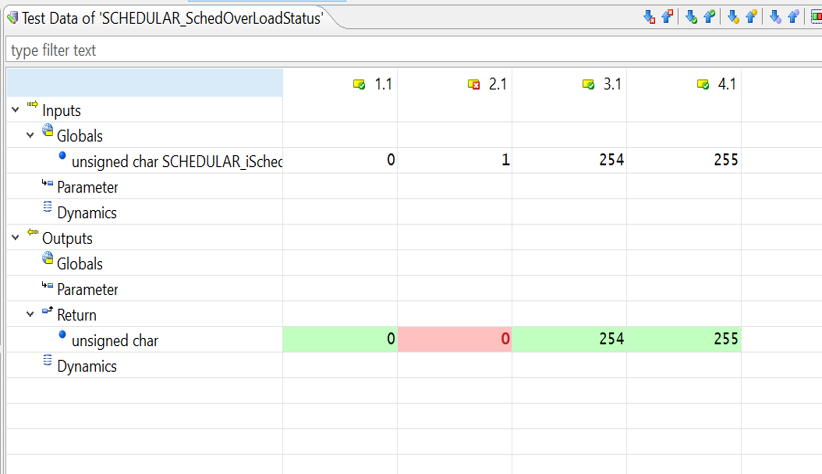
Step 2: Execution of the Test Cases in CANoe tool
- Now, the build with all the test cases will be run on the target ECU using the CANoe tool. CANoe acts a separate ECU that interacts with the target ECU and runs the test cases.
- The response from the target ECU is displayed on the CANoe tool and test reports are generated.
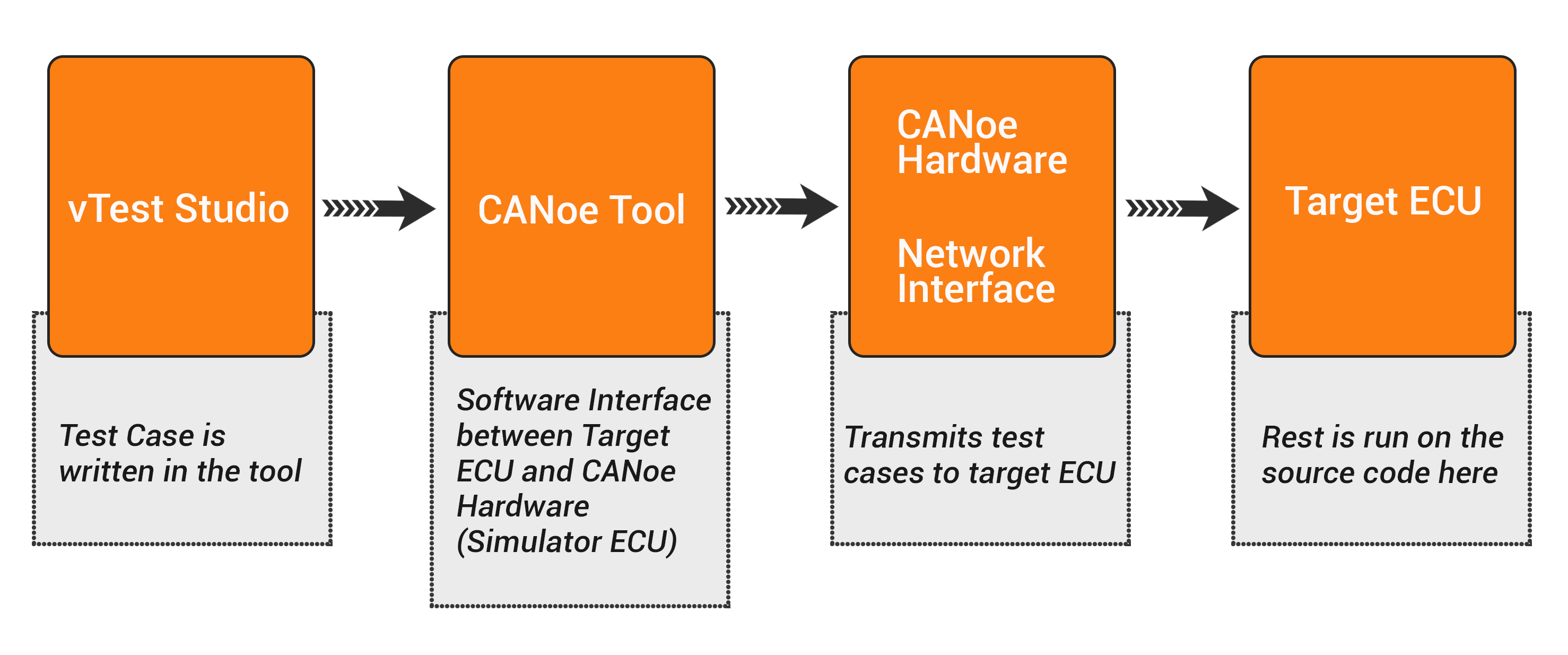
The point to be noted here is, that vTest Studio is used only for creating the test cases. These test cases are run on a separate tool called CANoe.
So, these two tools (vTest Studio and CANoe) complement each other in carrying out automation testing of an electronic control unit.
What are the Value-Adds of Using vTest Studio for Automation of Testing:
- vTest Studio can cater to a broad range of ECU applications, as this tool is equipped with several test-case editors
- The test sequences can be given parameters with scalar values, test vectors written in multiple test design languages like CAPL, C# etc.
- Test projects can be created and maintained in a simple manner using the user-friendly GUI
- vTest Studio offers universal traceability of the test specifications defined externally
- This automation testing tool can also provide high test coverage, without the need for writing any complex test case scripts
- vTest Studio supports Open Interface, this facilitates easy integration with other automation tools = like CANoe.
The Bigger Picture
The cost of implementing automation in testing, especially in case of an Embedded system, is high. However, from a long-term perspective and in terms of ROI, automation in testing is the need of the hour.
What automation testing can do in 1-hour, manual testing may take a week or so. Add to it the human error that might also delay the process and thus, increase the cost.
With automotive applications getting more software-centric, automation testing is the best way forward.
And thanks to automation testing tools like vTest Studio and CANoe, the process gets much simpler and less time-consuming.
All automotive stakeholders like OEMs, suppliers and technology providers benefit from the accuracy and lesser turn-around time made possible by automated testing of automotive ECUs (electronic control units).