FOTA Update | Firmware Over the Air - For IoT And Automotive Devices
Whether it is an automotive ECU product or field-deployed Industrial Automation devices, integration of Firmware over the Air / FOTA update feature has become a mission-critical process.
Firmware Over the Air update is necessary to ensure secure and robust operations of remote devices in Industry 4.0, automotive and healthcare domains.
Leverage our IoT and Automotive domain expertise of more than 12 years, for custom development of hardware and software components for FOTA update.
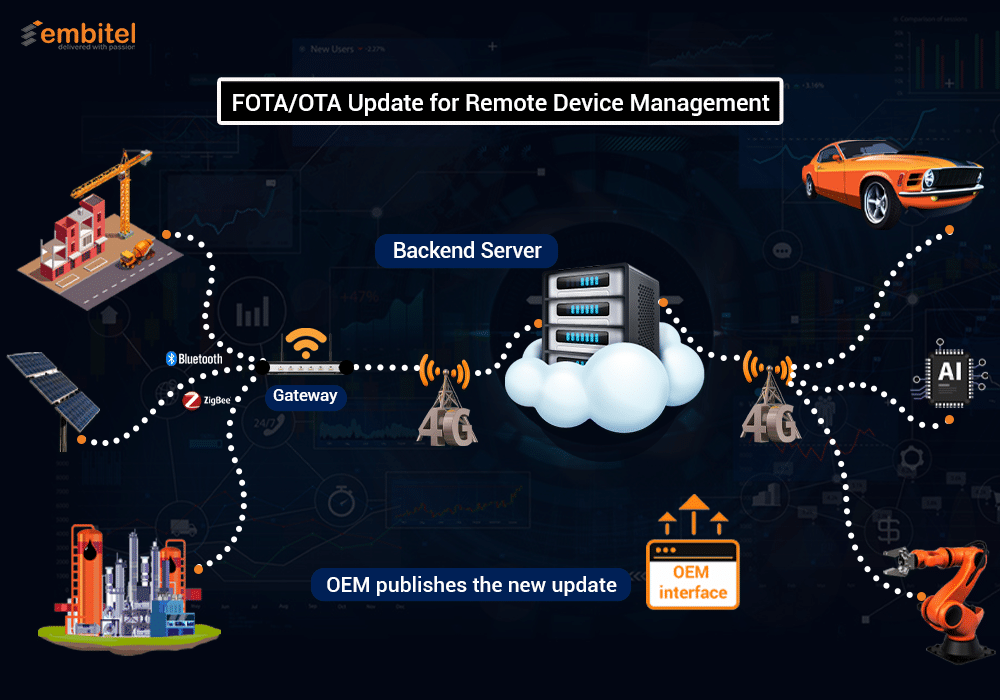
Features of Our FOTA Update Solution for Remote Device Management
Our end-to-end FOTA solution can be customised to facilitate the following:

- Remote device management through OTA software updates
<br\>
- Scheduling, release and reporting of the firmware build versions through a web server interface solution


Firmware Over the Air Integration – Services We Offer
- Flash Memory Selection – NOT, NAND & more, based on your project requirements
- Integration of Wi-Fi/Bluetooth/GPRS/GSM modules for secure communication between the FOTA server and the target devices.
- Design and development of Firmware and integration with IoT protocols such as MQTT, CoAP; HTTPS & SSL for secure data exchange; FTP/FTPS for file transfer.
- Selection of specific encryption methods to check the sanity of the update package.
- Deciding the level of FOTA update required (At the whole system level, OS and application level, or only at the application level).
- Bootloader development to enable firmware download and reprogramming on the application device.
- Design and development of the FOTA management server interface and other GUIs to build/schedule/deploy/manage the update package.
- Design and development of the interface (GUI) to build/schedule/deploy/manage the update package.
- Tracking as well as reporting the successful instances of firmware updates.
- Integration of Firmware Rollback mechanism to mitigate any failure or bug detected during Over the Air update.
- Development of Automated test frameworks to enable devices to perform self-test & send status reports, at the end of an update.
- Power Failure
- Communication Failure
- Memory Corruption
- Failure to boot the new firmware image
- Flashing of a corrupted firmware image
- Failure to retrieve the information about the configuration & last status of the firmware
- After design and development of the FOTA feature for your connected devices, the hardware and software components are subjected to the following pre-production test-case scenarios:
<br\>We also perform Image self-tests to check if all the firmware functions are working properly.
Meet Our IoT Leaders
[Video] What Makes Firmware Over the Air (FOTA) an Automotive Superhero?
Components of FOTA Update System
OTA Update for Your Connected System: Business Benefits
- Safeguard your applications against any possible security vulnerability
- Efficient and remote management of your critical work product and site equipment.
- OPTIMIZE DATA COSTS and minimize system downtime by updating numerous changes in one go, over the air.
- Update your firmware in line with your SCALING business.
- Reduce on-field MAINTENANCE COSTS by updating firmware on device, post-deployment
- With FOTA you can do:
- Feature updates
- Functional updates
Anytime, on Any number of connected systems.
FAQs Regarding FOTA/OTA Updates: IoT and Automotive Devices
- A. This decision regarding the method of firmware flashing will depend on the following factors:
- Number of devices to be updated ( A Gateway device is preferred if the number of deployed target devices is on the higher side)
- The type of communication interfaces available
- The operating environment of the deployed devices
- Desired cost-effectiveness of the FOTA feature
- A. We had ensured to make security features part of the FOTA solution at the design stage of the SDLC.
- Integrated HTTPS & SSL certifications: to ensure Secure data exchange
- Encryption Keys and security certificates for secure communication between server and target devices
- Role based Access Control to avoid any unauthorized data access
- Code Signing: to verify the authenticity and integrity of firmware executables and scripts and to safeguard them against any malicious tampering by unauthorized agents.
Following are the details regarding our Firmware –Over-The-Air (FOTA) security features:
- A. Based on our experience, a subscribe –publish mechanism for FOTA upgrade is ideal for large scale implementations. Additionally, a subscribe –publish mechanism offers following advantages over the Polling mechanism:
- Cost effective
- Minimizes data usage
Reason - field-deployed devices are not required to check for new firmware update every now & then . Any new firmware update package or image that gets published in the server, is notified to the devices as per the schedule.
Polling mechanism is easier to implement but consumes more data.
- A. The following components, of our FOTA reference design, can be reused in order to save development time and cost of your customized FOTA solution:
- Ready to deploy Bootloader Software
- Software components deployed for secure file transfer, update notifications.
- Reusable Algorithms for accurately
- updating the new firmware,
- Identifying the update requirements
- Validating the existing firmware versions
Additionally, Gateway device (Linux based) can also be reused if the target application is also based on Linux.
- A. IoT gateway devices that support firmware OTA flashing on connected devices can belong to one of the following categories:
- Processor and OS based Gateway: preferred for large scale (industrial) deployments. These are easily scalable and depend on application processor and the base OS ( Android/Linux).Cost of such IoT gateway devices is also comparatively higher.
- Microcontroller based Gateways: These are preferred for applications which require specific functionalities like - better device connectivity, reduced memory and power consumption; and involve lower BOM cost.
- Mobile Device as a Gateway: These are preferred when target devices are fewer in number and individually owned.
At Embitel, we have developed IoT gateway devices at various scales and for different application domains, specifically for telematics and industrial automation systems.
- A. Following are the architecture details regarding our OTA backend server:
- We have deployed Postgress relational database to leverage the following benefits:
- Open Source nature and support for an enterprise-class performance
- Cross platform compatibility ( UNIX, Windows, Native Windows)
- Responsive in high volume environments
- Exhaustive library and framework support
- Full database encryption to ensure security
- Our solution is backed by an Nginx server for file transfer. Our team took this decision based on the following features of an Nginx server:
- Versatile, efficient and light-weight web server
- Easy and simpler installations
- Ideal for serving static files pdf, zip, html, mp4 & others
- Support for high concurrent traffic
- Compatible with commonly-used web apps like WordPress, ruby, python, Joomla, drupal etc.
- We have also leveraged Django framework for developing interfaces for the target devices. The Django framework is known for its scalability, security and ease of execution - features that make it a favorite among the web developers.
- A. In order to ensure security of backend operations in the server and to avoid unauthorized access of the backend data, we implement:
- Password based authentication control, or
- Certificate based authentication (CA)
- A. All details related to firmware file and each of the versions (previous and the new) are stored systematically in the tables of the relational database.
The tables would include information such as the file name, the version number, and the action required (upgrade or delete) pertaining to each firmware package.
This ensures accurate version management of the firmware package, which is being deployed in the target devices.
In case a new version of the firmware has a bug or does not meet the desired expectations, there are provisions to roll back to the previous firmware version, using the information in the backend database.
- A. We use the Nginx server for backend operations which provides robust support for load balancing The NGINX server is an efficient (HTTP) load balancer, suitable for wide range of web applications.
The NGINX server has an event-driven (event as in any communication request) architecture that empowers it to manage thousands of connections within a single process with efficient use of hardware and memory.
Thus, even if the number of connected devices that needs a FOTA upgrade increases post initial-deployment, the NGINX server can easily process their connection request without creating traffic spikes.
- A. Our experienced solution development is a vibrant bunch of Industrial Automation and Automotive domain experts, with the following core skill-sets:
- Expertise in IoT communication protocols (MQTT, CoAP, HTTPS)
- Testing and validation expertise
- Experience in Bootloader Software Development
- Know-how and hands-on in system security best practices
Firmware Over the Air – Success Stories
FOTA Installation is a Three Step Process
- New update or the new version of the software/firmware is made available in the cloud server by the device owners.
- The latest firmware update is downloaded and made available to the network of the IoT or automotive devices ( e.g a Telematics unit in the car or a IoT enabled equipment in a manufacturing plant).
- The FOTA server stores all the information related to the devices in the network such as the current status, the existing version of the firmware in use, within a large database.
- The server also manages the process such as sending the firmware to the target application as and when they are published (or based on a schedule); Identifying any bug in the firmware, Reporting any fault or bug in the firmware code.
- The end devices or the application pull the upgrades from the server based on either the subscribe-publish mechanism or a polling mechanism over a secure wireless ( Wi-Fi/ BLE)connection.
- Installing new firmware and updating of software in the end-user application with the help of a bootloader